Imagine you’re sending money to a friend. You hit send, see the confirmation, and go about your day. But what if that transaction simply vanished? What if the network rewrote history to say you never sent it, allowing you to spend those same coins twice? This isn’t science fiction. It’s the reality of a 51% attack, and as of 2026, it is no longer just a theoretical risk for small projects-it is an active threat that has shaken major protocols.
The August 2025 attack on Monero was a wake-up call for the entire industry. For years, we assumed that controlling more than half of a blockchain’s computing power was economically impossible for anything but tiny altcoins. That assumption died when a single mining pool reportedly seized control of over 54% of Monero’s network, executing deep chain reorganizations and double-spending nearly $1 million worth of XMR. If it can happen to a privacy coin with a dedicated community, what keeps Bitcoin safe? And more importantly, how are developers building defenses for the future?
How a 51% Attack Actually Works
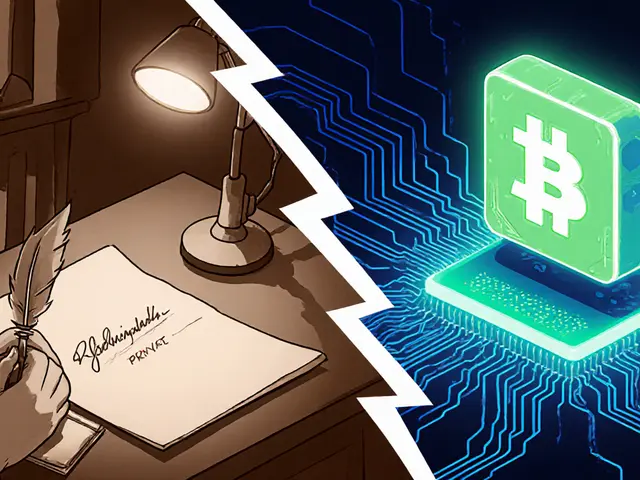
To understand the defense, you have to understand the weapon. In Proof-of-Work (PoW) blockchains like Bitcoin or Monero, miners compete to solve complex mathematical puzzles. The first one to solve it gets to add a new block of transactions to the ledger and receives a reward. The longest chain-the one with the most cumulative work-is considered the valid truth.
If a single entity controls more than 50% of the total network hash rate (computing power), they can mine blocks faster than everyone else combined. This allows them to:
- Double-spend: Send coins to a merchant, wait for a few confirmations, then secretly mine a longer version of the chain where that transaction never happened. The original payment is erased from the ledger, but the attacker still has the coins.
- Censor transactions: Refuse to include specific addresses in their blocks, effectively freezing assets.
- Reorganize the chain: Overwrite recent history, causing confusion and instability for users and exchanges.
Satoshi Nakamoto originally designed Bitcoin assuming that acquiring 51% of the network would be too expensive to be profitable. However, the economic landscape has shifted. As MIT Digital Currency Initiative researchers noted in 2025, attackers don’t always need to buy all the hardware upfront. They can rent hash power on services like NiceHash, turning a massive capital expenditure into a manageable operational cost for smaller chains.
The Monero Case Study: When Theory Became Reality
For most of 2025, 51% attacks were confined to obscure cryptocurrencies with market caps under $10 million. Then came August 2025. A mining pool named Qubic allegedly achieved 54.3% dominance over the Monero network. This wasn’t a glitch; it was a sustained assault.
Monero uses the RandomX algorithm, which was designed in 2019 specifically to resist ASICs (specialized mining chips) and favor CPUs. The goal was decentralization. Ironically, this design choice created a vulnerability. Because CPU mining is less efficient than ASIC mining, the total network hash rate remained relatively low-around 2.1 GH/s compared to Bitcoin’s massive scale. This made the target cheap enough to hit.
During the attack, Qubic executed 14 confirmed double-spend transactions totaling 1,842 XMR. They also performed deep reorganizations, reversing up to 1,200 blocks. The immediate impact was severe: Monero’s price dropped 22.7% within 72 hours, and users faced significant transaction delays. The incident proved that even well-designed algorithms cannot protect a network if the economic barrier to entry is too low.
| Metric | Bitcoin | Monero |
|---|---|---|
| Network Hash Rate | 650 EH/s | 2.1 GH/s |
| Estimated Attack Cost (Hardware) | $12.7 Billion | Under $100,000 (via rental) |
| Daily Electricity Cost | $48 Million | Minimal |
| Consensus Algorithm | SHA-256 (ASIC optimized) | RandomX (CPU optimized) |
| Vulnerability Status | Extremely Low | High (demonstrated in Aug 2025) |

Why Bitcoin Remains Safe (For Now)
While Monero suffered, Bitcoin stood firm. As of early 2026, Bitcoin’s network hash rate sits at approximately 650 exahashes per second (EH/s). To put that in perspective, Bitcoin accounts for 98.7% of the total proof-of-work hash rate across all major cryptocurrencies. Trying to attack Bitcoin today is like trying to sink an aircraft carrier with a handgun.
The cost is prohibitive. Acquiring the necessary hardware alone would cost around $12.7 billion. On top of that, the daily electricity bill to run such an operation would exceed $48 million. Unless the attacker intends to destroy Bitcoin’s value entirely (which would render their stolen coins worthless), the economics do not work. This is known as "economic finality."
However, safety is not guaranteed by size alone. It also relies on distribution. In 2025, the top five mining pools-Foundry USA, Antpool, F2Pool, ViaBTC, and Binance Pool-collectively controlled 63.2% of the hash rate. While this sounds concentrated, individual miners can switch pools quickly. Data shows that miners can migrate to a different pool within an average of 7.3 minutes if suspicious activity is detected. This fluidity prevents any single pool from holding permanent majority control without triggering a defensive response from the rest of the network.
New Defense Strategies for 2026
The industry has learned hard lessons from the Monero incident. Developers and enterprises are no longer relying solely on raw hash rate. They are implementing layered security strategies.
Real-Time Monitoring and Alerts
By Q2 2025, 78% of the top 50 proof-of-work chains had implemented real-time monitoring systems. These tools track hash rate concentration continuously. If a single pool exceeds 40% of the network’s power, alerts are triggered. This gives nodes and exchanges time to react, such as increasing confirmation requirements or pausing withdrawals.
Adaptive Confirmation Thresholds
Historically, six confirmations were considered safe for Bitcoin. Today, that standard is dynamic. Proposed updates like Bitcoin Improvement Proposal (BIP) 342 introduce "Adaptive Confirmation Thresholds." For small transactions, six confirmations might suffice. For large transfers over $1 million, the system may demand 50+ confirmations. This reduces the window of opportunity for an attacker to reverse a high-value transaction before it becomes irreversible.
Fibonacci Checkpoints
Some developers are exploring modified consensus rules, such as "Fibonacci checkpoints." These mechanisms exponentially increase the computational cost required to reorganize the chain as you go further back in time. This makes deep-chain attacks (like the 1,200-block reversal seen in Monero) mathematically impractical, even if the attacker briefly holds 51% power.
Geographic Decentralization
Successful networks now aim to keep hash rate distribution below 35% in any single country. This ensures that political instability or regulatory pressure in one region does not compromise the global network’s integrity.
Risks for Layer-2 Solutions and Enterprises
You might think moving off-chain solves the problem. Not necessarily. Layer-2 solutions like the Lightning Network rely on the base layer for final settlement. If a 51% attack occurs on Bitcoin, an attacker could reverse on-chain transactions that close Lightning channels. Lightspark researchers simulated this in March 2025 and found that an attacker could potentially steal $14.3 million in channel balances by exploiting this dependency.
Enterprises have adapted their internal security practices in response. By 2025, 83% of major cryptocurrency exchanges implemented multisignature hot wallet architectures, up from 47% in 2024. They also conduct mandatory bi-weekly security audits. Despite these measures, Chainalysis reported $2.17 billion stolen from services in 2025 through various vectors, including compromised credentials and smart contract bugs. Direct 51% attacks accounted for 17% of these losses, highlighting that while rare, they remain a potent threat vector for smaller assets.
The Future Consensus Landscape
The era of pure Proof-of-Work is evolving. We are seeing a shift toward hybrid models and alternative consensus mechanisms that reduce the risk of centralization.
Ethereum’s transition to Proof-of-Stake (PoS) eliminated the 51% hash rate risk entirely, replacing it with stake-based security. However, PoS introduces different risks, such as long-range attacks. For PoW chains, the future may lie in hybrid approaches. Ethereum’s proposed "Hybrid PoW/PoS Fallback" mechanism, slated for a Q2 2026 upgrade, aims to combine the security benefits of both models. Similarly, academic research from MIT DCI is exploring "Proof-of-Stake Bridging" for existing proof-of-work chains, allowing them to leverage staking security without abandoning their legacy infrastructure.
Regulatory pressure is also intensifying. Following the Monero attack, the U.S. SEC issued "Guidance on Proof-of-Work Network Security" in June 2025. This guidance requires exchanges to disclose hash rate concentration risks to investors. This transparency forces projects to prioritize network health and decentralization, as poor security metrics can lead to delisting or legal scrutiny.
Looking ahead, the consensus among experts is clear: economically viable 51% attacks will persist for coins under $500 million market cap. For these projects, the choice is stark. They must either transition to alternative consensus mechanisms, implement centralized checkpointing systems (which compromises decentralization), or accept the inherent risk. For giants like Bitcoin, the path forward is continuous optimization of monitoring, adaptive thresholds, and maintaining the astronomical economic barrier to entry.
Can Bitcoin suffer a 51% attack?
It is highly unlikely. As of 2026, Bitcoin's hash rate is 650 EH/s, requiring an estimated $12.7 billion in hardware and $48 million daily in electricity to attack. The economic cost far outweighs the potential profit, making it economically unfeasible unless the attacker intends to destroy Bitcoin's value entirely.
What happened during the Monero 51% attack in 2025?
In August 2025, a mining pool named Qubic reportedly gained control of 54.3% of Monero's hash rate. They executed 14 double-spend transactions totaling 1,842 XMR and reorganized up to 1,200 blocks. This caused a 22.7% price drop and significant transaction delays, demonstrating that CPU-minable networks are vulnerable to rented hash power.
How can I protect my transactions from a 51% attack?
For high-value transactions, wait for more confirmations than usual. While six confirmations are standard for Bitcoin, larger amounts may require 50+. Use wallets that monitor network health and consider using Layer-2 solutions only after ensuring the base layer is secure. Always verify the current hash rate concentration of the network you are using.
Are Layer-2 solutions like Lightning Network safe from 51% attacks?
Layer-2 solutions are indirectly vulnerable. If the underlying blockchain (e.g., Bitcoin) suffers a 51% attack, an attacker could reverse on-chain transactions that settle Layer-2 channels. Simulations show this could lead to significant theft of channel balances, so the security of the base layer is critical.
What is the role of real-time monitoring in preventing attacks?
Real-time monitoring systems track hash rate distribution across mining pools. If a single pool exceeds 40% of the network's power, alerts are triggered. This allows nodes and exchanges to take preventive actions, such as increasing confirmation requirements or pausing operations, before an attack can succeed.